Hey!
I’m sorry that I haven’t been able to post more in this blog for the past 2 months, personal projects, exams, life and work came up, it was pretty overwhelming.
Let’s talk about one of them now, shall we? Piano Hacking.
I’ve spent on what I thought would be a cool one week off project some time up
until I’ve proposed a talk to the CCC! Unfortunately…
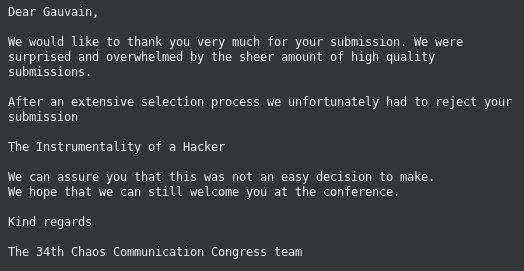
Yup...
I got rejected.
So why was I? I have a few theories, as I can already say, a talk about Hacking
subways and voting machines have both been rejected, from people with work I can trust.
So that doesn’t mean the idea was bad in itself,
as hacked voting machines would quite literally allow FAKE ELECTIONS.
So next down on the list is the overwhelming list of proposals:
[more than 70% rejection rate for the security
track alone!] (https://twitter.com/iamnion/status/932591686118772736) As
organizers said this could be due to the fact that there were so many proposals
this year they had to get rid of some, which could make this talk about Tamagotchis much harder to be accepted.
And finally my lack of experience in the domain of public talks.
Learning from all of this I can say I’m not even mad, at worse I’m just in a mood thinking: “Well too bad for them”.
Have I given up yet though? No, of course not!
Instead of doing a purely verbal project I am splitting up my time to make it more learning-friendly. As most of you already know I rarely do things for only one goal and this project is surely not an exception.
So without further ado let me introduce you to what’s going to happen:
“The Instrumentality of a Hacker ~ Introduction to Hardware Hacking”
My current plan is to make a video on this matter, showing the global idea of what Hardware Hacking is in a practical view and allow everyone to understand the complete process without dumbing it down, which is what most writings about the subject do by centralizing what they think the hardest parts were.
The video itself will have two goals acknowledged: To introduce piano hacking through a project I’ve worked on (and that, hey, music is still a thing), and to teach hardware hacking.
Now then have I given up on the CCC too? No! I have the pleasure to announce I’ll be doing a lightning talk (at the very least) at the CCC this year! While Lightning talks proposals and so on haven’t been announced yet I have scripted most of the video and am just missing the material to film it currently, so I can say that with good luck this is going to be a thing!
I’ll also publish an article there on the project on top of the rest with added written notes and the entire script.
Now that this is taken care of, as some of you know, I have more than 6 articles currently in the waiting list. Now why are they? Either they are a rant, which is not the best idea for a blog supposed to talk about tech, or they are not tech, which, while I like the matter, feel I should introduce first by yet another article on the matter, which is a rant and requires another post to be written.
Basically a lot of circular dependencies :D
But everything is finally getting together! After I am done with my math exam this week I should finally have the time to work on everything, and let’s hope I can share some other projects after that!
On those words have a good travel through life Sir, as I currently am writing my future.
P.S: As I won’t make a major use of the preliminary proposal I’ve done for the CCC here it is, in its non peer reviewed or checked beauty!
Title=The Instrumentality of a Hacker
Subtitle=Hacking a piano for fun and profit
Event type=Lecture
Track=Security
Time Slots=1:00
Language=English
Event classifiers:
Prior Knowledge=30%
Defense - Offense=90%
Security=100%
Hardware=60%
Abstract=Pianos are one of the most used instruments, and even moreso in the music composition world. Electronic pianos, especially MIDI keyboards, are a target of choice as they are usually directly connected through USB to a computer. This allows us to pull off some neat tricks if we can get control of this piano or even permitting us to take control of the MIDI device altogether! This talk covers my attempts at taking full control of my keyboard, reversing it and weaponizing it.
Description=While a piano may sound simplistic in structure, having few keys and buttons that should send data, the truth is more and more of a recent piano is composed of electronics. These force us to interact with a black box, which is executing more than you would think. Thanks to what is hidden from us, a piano could easily be used to take control over ones computer unknowingly. I will try to show how we can understand and make use of this blackbox and the potential consequences of forgetful decisions.